Legal Responsibilities for CMAAs: Comprehensive Interactive Guide
Legal responsibility shows up in ordinary moments long before it shows up in a complaint, a denial, an audit, or a patient grievance. A CMAA touches scheduling, registration, privacy, records, communication, documentation flow, billing support, and escalation. Each one carries legal weight when handled carelessly.
This guide breaks those responsibilities into daily actions you can recognize fast, apply cleanly, and defend under pressure while strengthening the same operational skills behind patient record updates and EMR compliance, patient privacy communication essentials, insurance verification, and top HIPAA terms for CMAAs.
1. Why Legal Literacy Changes a CMAA’s Value Immediately
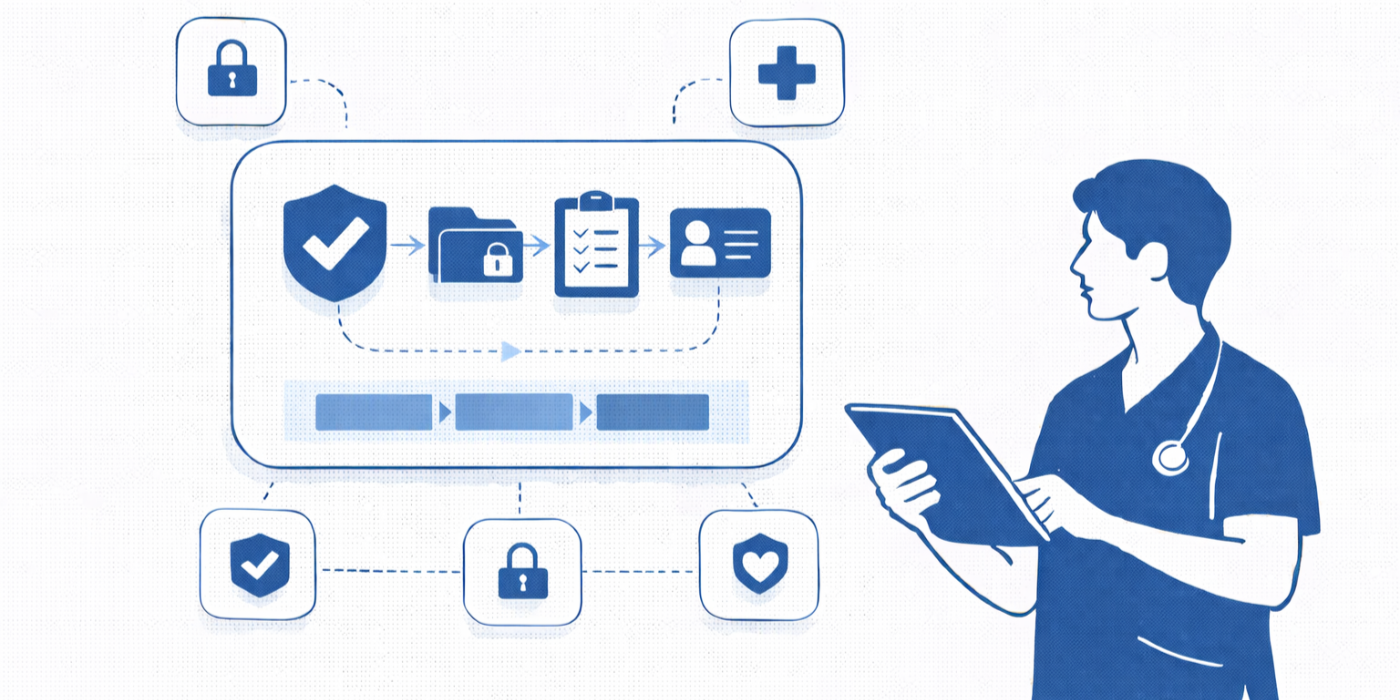
A CMAA does far more than move paperwork. The role often becomes the first line of protection between patient information, office workflow, payer rules, and regulatory exposure. Federal privacy law applies to covered health care providers that conduct certain electronic transactions, and those rules sit alongside security safeguards for electronic protected health information and notice obligations that shape how patients are informed about privacy practices. A CMAA may not write the policy, yet the CMAA often becomes the person who either protects the workflow or weakens it through a rushed shortcut inside front desk operations, healthcare portal use, EMR integration workflows, secure patient scheduling tools, and medical admin collaboration systems.
That is why legal literacy changes career value so quickly. A CMAA who understands privacy limits, minimum necessary thinking, record-access rights, communication requirements, and documentation integrity stops preventable problems before they become expensive ones. Patients also generally have a right to inspect or obtain copies of their health information, and providers generally have up to 30 days to respond in most cases. That means one sloppy records-release step, one careless hallway conversation, or one wrong portal message can create operational and legal fallout at the same time. Those risks connect directly to tools for efficient medical records release, active listening techniques, effective patient communication terms, medical admin time tracking, and future-proof CMAA skills.
Legal literacy also protects the office from quieter failures that rarely feel dramatic in the moment. A patient gets asked for more information than the task requires. A family member receives a casual verbal update without proper verification. A self-pay patient is scheduled without the office thinking through good faith estimate obligations. An interpreter need gets treated as a convenience issue instead of an access issue. Each one feels small when the desk is busy. Each one becomes serious when the facts are reviewed later. Offices that treat law as workflow design perform better in the same way offices improve through appointment scheduling best practices, managing difficult patient conversations, de-escalation techniques, resolving EMR software issues, and AI and automation in medical administration.
| # | Legal Responsibility Area | What It Means in Daily CMAA Work | What to Verify First | Risk If Ignored |
|---|---|---|---|---|
| 1 | Patient identity verification | Confirming the right patient before discussing care, scheduling, releasing records, or portal support. | Name, DOB, approved identifiers, practice policy. | Wrong-patient disclosure or chart action. |
| 2 | Minimum necessary access | Only opening or sharing information needed for the task at hand. | Role need, task purpose, access level. | Unnecessary PHI exposure. |
| 3 | Verbal privacy | Controlling what is said at the desk, in hallways, on speakerphone, or in waiting areas. | Who can hear, who is present, what is needed. | Privacy complaints and trust damage. |
| 4 | Screen privacy | Protecting EMR screens, portal views, printouts, and shared workstations. | Logged-in status, monitor angle, logout habits. | Unauthorized viewing of PHI. |
| 5 | Notice of privacy practices workflow | Making sure patients receive required privacy information according to office workflow. | First-service process, acknowledgment method. | Broken intake compliance trail. |
| 6 | Record access requests | Routing patient requests to inspect or obtain copies correctly and promptly. | Identity, request format, destination, scope. | Delay, complaint, legal exposure. |
| 7 | Records release authorization | Using the right release process before sending records to outside parties when required. | Authorization validity, recipient, date range, content requested. | Improper disclosure. |
| 8 | Portal messaging boundaries | Sharing only appropriate details through secure channels and the right account. | Correct patient account, message content, urgency. | Privacy breach or delayed care. |
| 9 | Phone disclosure controls | Avoiding casual disclosures to unverified callers or relatives. | Caller verification, disclosure permissions, purpose. | Improper verbal disclosure. |
| 10 | Email handling | Using approved communication channels and recipient checks. | Encryption policy, recipient accuracy, attachment review. | Misdirected PHI. |
| 11 | Interpreter access | Helping patients receive effective communication support when needed. | Language or disability-related communication need, office process. | Access barriers and civil-rights exposure. |
| 12 | Nondiscrimination workflow | Treating patients consistently across protected categories and access needs. | Scheduling access, communication support, complaint routing. | Disparate treatment concerns. |
| 13 | Consent support accuracy | Routing consent forms, signatures, and visit prep through the correct workflow. | Form version, patient identity, provider process. | Invalid or incomplete documentation. |
| 14 | Scope-of-role boundaries | Avoiding legal or clinical overreach in advice, diagnosis language, or medical judgment. | What the role permits, when to escalate. | Unauthorized practice risk. |
| 15 | Documentation integrity | Entering, correcting, and routing chart information accurately and transparently. | Source of information, timestamp, who requested update. | Audit issues and patient harm. |
| 16 | Amendment requests | Recognizing when a patient seeks record correction and routing properly. | Nature of request, office policy, record owner. | Improper chart changes. |
| 17 | Scheduling fairness | Applying consistent access rules without selective gatekeeping. | Template rules, urgency criteria, payer-neutral process. | Complaint patterns and inequity. |
| 18 | Good faith estimate support | Helping uninsured or self-pay patients receive correct estimate workflow. | Coverage status, scheduled service, timing. | Billing disputes and compliance issues. |
| 19 | Billing data accuracy | Passing clean demographic, insurance, and service-support details downstream. | Policy details, authorization status, visit type. | Denials and false claim risk. |
| 20 | Fraud red-flag escalation | Escalating suspicious identity, billing, documentation, or access activity. | Pattern, evidence, internal reporting chain. | Loss, abuse, and audit exposure. |
| 21 | Incident reporting | Reporting privacy mistakes, lost documents, wrong faxes, or portal errors immediately. | What happened, who was affected, when it occurred. | Late containment and bigger damage. |
| 22 | Password and login discipline | Using unique access credentials and secure login habits. | User identity, session timeout, shared-device rules. | Accountability failure and security weakness. |
| 23 | Paper record control | Handling printouts, labels, forms, and scans securely. | Pickup location, shred process, scan destination. | Physical PHI exposure. |
| 24 | Vendor and fax destination checks | Confirming recipient accuracy before transmission. | Fax number, email, outside office identity. | Misdirected protected information. |
| 25 | Complaint intake | Receiving privacy, access, billing, or discrimination concerns without defensiveness. | Facts, timing, patient concern, escalation path. | Escalated conflict and missed remediation. |
| 26 | Telehealth privacy support | Helping remote workflows preserve identity, confidentiality, and accurate routing. | Patient account, contact method, environment guidance. | Wrong-person access or improper disclosure. |
| 27 | Retention and destruction process | Following office rules for storage, scanning, and disposal instead of ad hoc decisions. | Record type, retention rule, approved disposal method. | Premature destruction or uncontrolled storage. |
| 28 | After-hours message handling | Managing voicemail, portal, and callback workflows without unsafe disclosure. | Urgency, callback identity checks, routing protocol. | Privacy mistakes and delayed escalation. |
| 29 | Third-party request scrutiny | Recognizing when outside requests need formal review instead of desk-level release. | Requester identity, legal basis, authorization status. | Improper disclosure or obstruction. |
| 30 | Training accountability | Keeping up with policy updates, role-specific workflows, and required compliance education. | Latest policy, version control, supervisor expectations. | Repeated preventable errors. |
2. The Legal Duties Every CMAA Should Map Directly to Workflow
The first duty is privacy discipline. HIPAA’s Privacy Rule sets national standards for protected health information, while the Security Rule requires administrative, physical, and technical safeguards for electronic PHI. For a CMAA, that translates into practical behavior: verify identity before discussing a chart, limit what you access, protect screens and printouts, avoid casual disclosures, and route records correctly every time. Legal responsibility becomes easier to manage when it is built into top EMR shortcuts for productivity, EMR issue resolution, healthcare CRM workflows, interactive guide to emerging medical admin technologies, and directory of medical admin staff scheduling tools.
The second duty is access and release accuracy. Patients have rights over their health information, and offices need reliable processes for inspection, copies, and permitted disclosures. A CMAA does not get to improvise because the waiting room is full or because a caller sounds convincing. The job is to follow the release path, verify the person, confirm the scope, and escalate when the request is outside the desk’s authority. That responsibility overlaps with tools for efficient records release, healthcare portal terms, patient privacy communication essentials, interactive training on patient record updates, and top HIPAA terms for medical scribes.
The third duty is equal access and communication. Section 1557 prohibits discrimination on the basis of race, color, national origin, sex, age, or disability in certain health programs and activities, and the ADA requires effective communication for people with disabilities. Covered entities generally cannot require a patient to bring their own interpreter. For a CMAA, this changes the way scheduling, intake, reminders, waiting-room interaction, and complaint handling should work. Civil-rights compliance becomes concrete through active listening techniques, effective patient communication terms, de-escalation techniques, empathy in healthcare administration, and interactive guide to handling scheduling conflicts.
The fourth duty is financial and documentation integrity. When an uninsured or self-pay patient is scheduled, the office may need to support good faith estimate workflows. When information enters the chart, it must be traceable, accurate, and routed properly. When billing-related data moves downstream, the front-end facts must still be clean. That is where legal responsibility meets operational competence inside top medical billing terms all CMAAs should understand, insurance verification examples, patient communication apps, medical appointment scheduling tools, and virtual medical administration trends.
3. HIPAA, Records, Access Rights, and Release Errors That Hurt Offices Fast
Most CMAA legal mistakes do not start with bad intent. They start with speed. Someone wants help right now. A parent sounds urgent on the phone. A spouse steps up to the desk sounding fully informed. A provider asks for a fast printout while two more patients check in. A portal message looks harmless. Under pressure, people often substitute familiarity for verification. That is exactly where privacy failures begin. The minimum necessary standard exists because healthcare teams need a discipline stronger than instinct. The question is never “Do I basically know this person?” The question is “What is required for this disclosure, this task, this chart action, and this channel?” That mindset grows stronger through top HIPAA terms for CMAAs, patient privacy communication essentials, front desk operations guidance, healthcare portal definitions, and EMR compliance training.
Records requests create a second cluster of legal risk. Patients generally have access rights, and offices need reliable routing, documentation, and turnaround processes rather than ad hoc desk decisions. Trouble begins when staff confuse “helpful” with “authorized.” A request for the entire chart gets handled like a request for a lab result. A third-party request gets treated like a patient request. A message asking for records is answered inside an insecure or mismatched account. Those failures damage trust first and compliance second, which makes them harder to repair because the patient often remembers the office as careless long after the technical issue is fixed. That is why strong offices pair tools for records release, healthcare CRM literacy, patient communication apps, collaboration tools for office teams, and medical admin professional organizations with stricter identity and release workflows.
Electronic mistakes carry their own legal signature. The Security Rule requires safeguards for electronic PHI, which means the problem is never limited to hackers or major cyber events. A sticky note password, a shared login, an unlocked workstation, a wrong attachment, a fax sent to an old number, or a chart left open at a registration desk can expose the office just as fast as a more dramatic incident. Unique user identification and role-based access controls matter because accountability collapses when nobody can tell who actually accessed or changed the record. This is where EMR integration tools, medical admin collaboration tools, interactive guide to emerging technologies, secure scheduling tools, and AI and automation guidance become compliance tools rather than convenience tools.
4. Communication, Consent Support, and Civil-Rights Access Are Legal Work Too
Many CMAAs think of law as a privacy subject. In reality, communication can become a civil-rights issue just as quickly. Section 1557 protections and ADA effective-communication requirements matter at first contact, not after a complaint arrives. A patient who needs a qualified interpreter, accessible communication support, or language assistance should not experience that need as an inconvenience the office resents. Access must be built into the workflow itself. That changes how reminders are sent, how consent is explained, how forms are offered, how scheduling barriers are handled, and how complaints are received. These duties connect naturally to empathy in healthcare administration, effective patient communication, active listening techniques, de-escalation techniques, and handling difficult conversations with patients.
Consent support deserves equal care. A CMAA often guides form flow, verifies identities, answers process questions, and routes the patient toward the right next step. Legal trouble starts when support turns into overreach. Explaining process is part of the role. Interpreting clinical meaning, improvising medical advice, or pushing a patient toward a decision falls outside safer administrative boundaries. The role becomes stronger when the CMAA learns the exact line between explaining what the office needs and explaining what only a clinician or authorized decision-maker should explain. That distinction strengthens work done through patient intake procedures, appointment scheduling best practices, front desk operations, telehealth platform definitions, and future-proof CMAA career planning.
A legally strong office also avoids selective friction. Patients should not have an easier or harder path to scheduling, communication, complaint handling, or payment explanation because of language, disability, age, sex, race, national origin, or who they seem to be. Bias in healthcare administration often hides inside workflow variation: one patient gets a careful explanation, another gets brushed off; one patient receives clear portal help, another gets told to “figure it out”; one patient’s communication barrier gets solved quickly, another is treated like a burden. CMAAs protect the office when they apply the process consistently and escalate barriers early using patient communication apps, scheduling conflict workflows, emergency appointment management, medical admin communities and forums, and networking strategies for medical admin professionals.
5. Billing Integrity, Documentation Integrity, Scope Boundaries, and Incident Reporting
Billing risk often begins before the bill exists. A self-pay patient may need a good faith estimate workflow. An insurance detail entered carelessly may push the visit down the wrong path. An authorization mismatch may sit unnoticed until after service. A demographic error may break claim follow-up and patient communication together. That is why legally safer billing support depends on stronger front-end habits inside insurance verification, top medical billing terms for CMAAs, medical office automation trends, medical administration report insights, and new-study healthcare efficiency gains from certified CMAAs.
Documentation integrity carries a different kind of legal weight. A CMAA may enter demographic updates, route amendments, queue forms, upload records, or support encounter preparation. Every one of those actions becomes part of the office’s defensibility when facts are reviewed later. Trouble appears when staff “clean up” a chart without traceability, guess at information the patient did not confirm, or update the wrong record because the desk is moving too fast. Legally safer chart work depends on respecting timestamps, source clarity, account integrity, and escalation boundaries. That is why the role gains strength from interactive training on patient record updates, EMR shortcuts, resolving common EMR issues, healthcare portal workflows, and directory of EMR/EHR platforms.
Scope boundaries protect careers. A legally strong CMAA does not diagnose, does not guess at clinical meaning, does not promise coverage, does not improvise consent language, and does not decide alone when a questionable disclosure is acceptable. The role gets more respected, not less, when escalation happens early and precisely. That habit matters most in the ugly moments: the angry family member demanding updates, the patient pushing for advice the CMAA cannot provide, the provider asking for a rushed workaround, the wrong fax that “probably went nowhere,” the portal message sent to the wrong account, the lost printout, the unlocked workstation, the suspicious access pattern. Under HIPAA’s Breach Notification Rule, significant breaches can trigger strict reporting obligations for covered entities, including notification to HHS in certain cases within defined time frames, which is exactly why front-line staff should escalate incidents immediately instead of trying to quietly fix them alone. That operational discipline belongs beside de-escalation training, handling difficult conversations, medical admin collaboration tools, professional organizations, and future-ready CMAA skills.
6. FAQs
-
The most common pattern is skipping verification because the workflow feels familiar. Staff recognize the family, the phone number, the portal tone, or the visit history and start acting before identity, authority, or channel rules are confirmed. That habit creates privacy risk at the desk, on the phone, through portal messaging, and during records release. Stronger habits come from front desk operations training, patient privacy communication essentials, healthcare portal workflows, and interactive EMR compliance training.
-
A CMAA can explain process, office workflow, next steps, and where the patient should direct the question. Clinical interpretation belongs with the appropriate clinician or authorized decision-maker. Keeping that line clear protects the patient and protects the CMAA’s role. This boundary becomes easier to manage through effective patient communication terms, active listening techniques, patient intake procedures, and future-proofing your CMAA career.
-
Think in sequence: verify identity, confirm the type of request, confirm whether the request comes from the patient or another party, route it through the approved release path, and document the handoff. Patients generally have access rights to their records, and providers generally must respond within the HIPAA time frame in most cases. That makes routing accuracy essential. Related training lives in tools for records release, patient privacy communication essentials, healthcare CRM reference, and healthcare portal terms.
-
Treat them as access obligations built into workflow, not optional add-ons. Section 1557 and ADA effective-communication requirements can affect scheduling, registration, communication, forms, complaints, and patient understanding. A patient generally should not be forced to bring their own interpreter as the office’s default solution. Stronger preparation comes from empathy in healthcare administration, de-escalation techniques, handling difficult patient conversations, and appointment scheduling best practices.
-
Because financial communication can trigger regulatory duties and dispute exposure. Self-pay and uninsured workflows may require good faith estimate support, and inaccurate front-end information can contaminate the entire downstream billing process. That is why legal safety and revenue-cycle discipline overlap inside insurance verification, top billing terms for CMAAs, medical appointment scheduling tools, and secure patient scheduling tools.
-
Escalate immediately through the office’s incident path. Do not guess, hide, delay, or “quietly fix” the issue without reporting it. Fast internal escalation gives the organization the best chance to contain harm, investigate accurately, and meet any required response obligations. That mindset aligns with EMR issue resolution, medical admin collaboration tools, professional organizations, and future-ready CMAA skills.